Automated Firewall Policy Validator
Issued at
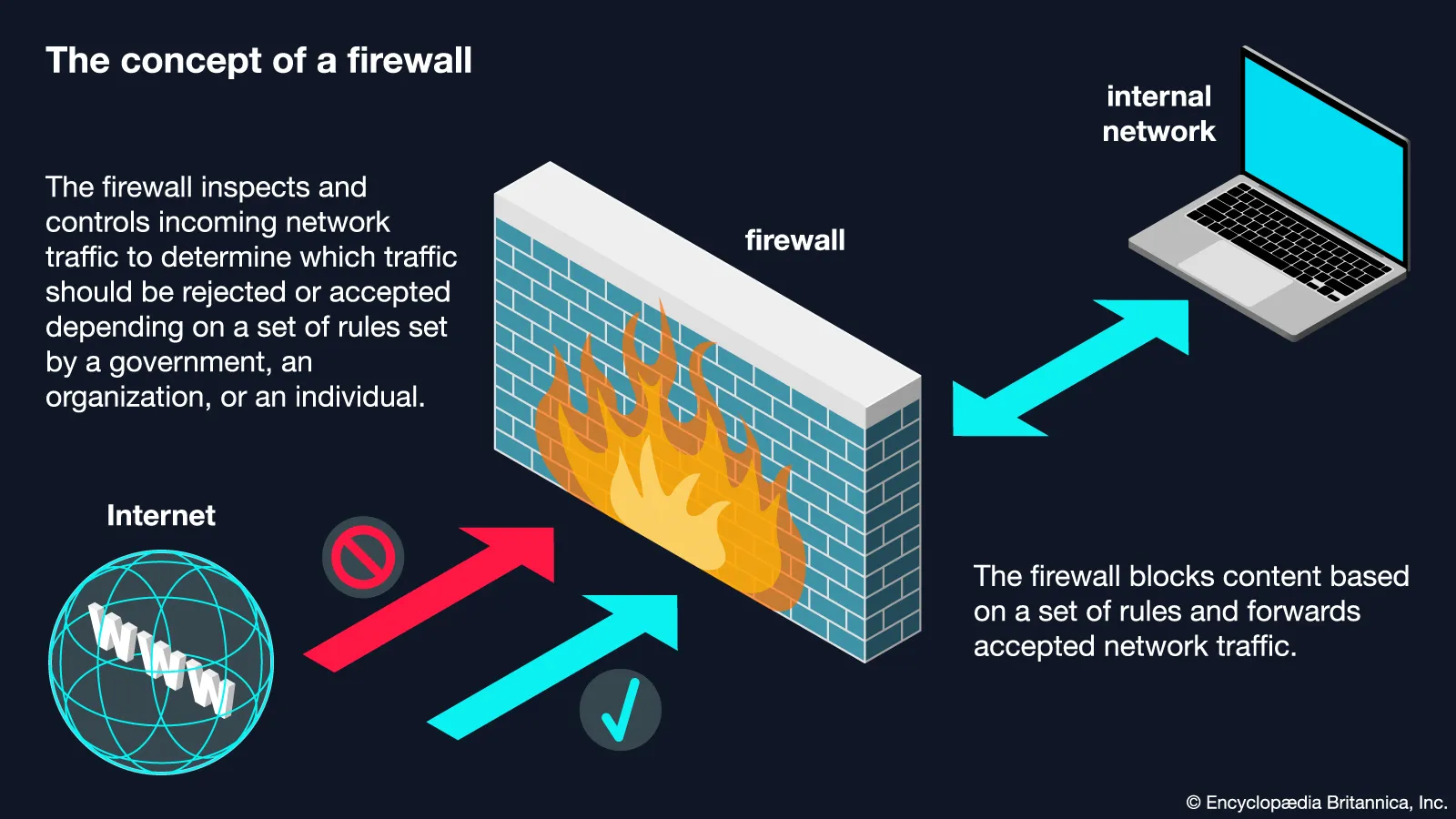
March, 2026 This is a network automation tool proposed to Nagad Ltd. to quickly check whether a newly proposed firewall rule already exists in the current policy. This reduces duplicates, speeds up reviews, eliminates human error, and keeps the policy clean. It validates whether newly proposed security policies already exist. If it exists, the requester will not apply for it. If it does not exist, the requester can proceed. Built entirely in‑house, the tool enhances operational efficiency, strengthens policy validation workflows, and contributes to maintaining a resilient organizational security posture. As a result, this reduces duplicates, speeds up reviews, eliminates human error, and keeps the policy clean.
Link: Get The Source Code
Technologies Used
Python REST API
DOS Attack - Email Bombing
Issued at
September, 2024 An email bomb is a denial-of-service attack that involves sending large volumes of messages to an email address. Email bombing usually aims to render the victim’s email unusable or hide important messages (such as security breach alerts) in the torrent. The recipient of an email bomb may not be the attacker’s intended victim — criminals can also flood random mailboxes with junk to bring down the server hosting them.
Link: Get The Source Code
Technologies Used
Python
Malware - Ransomware
Issued at
September, 2024 Ransomware is malware that employs encryption to hold a victim’s information at ransom. A user or organization’s critical data is encrypted so that they cannot access files, databases, or applications. A ransom is then demanded to provide access. It is a cryptography based attack.
Link: Get The Source Code
Technologies Used
Python
Spyware - Keylogger
Issued at
September, 2024 A keylogger, sometimes called a keystroke logger, is a type of surveillance technology used to monitor and record each keystroke on a specific device, such as a computer or smartphone. It can be either hardware- or software-based. The latter type is also known as system monitoring software or keyboard capture software.
Link: Get The Source Code
Technologies Used
Python
Brute Force Attack - Dictionary Attack
Issued at
September, 2024 A brute force attack is a trial-and-error method used to decode sensitive data. The most common applications for brute force attacks are cracking passwords and cracking encryption keys.
Link: Get The Source Code